Last year, attentive members of the public forwarded no less than 6 million messages to suspicious@safeonweb.be. That information allowed us to get more than 650,000 suspicious links blocked. Less attentive Internet users who then clicked on those links were redirected to a warning page instead of getting scammed.
All these emails enable us to publish weekly alerts on Safeonweb.be, our Facebook page and our Twitter account. We also send these messages via the Safeonweb App. In 2022, we published more than 80 alerts about the most common current phishing messages.
Energy crisis inspires scammers
Whereas in 2021 and early 2022 many phishing messages exploited the pandemic to attract people's attention (ordering face masks, signing up for COVID vaccines or boosters, etc.) the main topic for the remainder of 2022 was the energy crisis: messages offering energy allowances or premiums came in all forms (email and text messages) and the number of fake web shops offering cheap pellets skyrocketed.
These are financially difficult times for everyone and so many people dream of getting rich quick. So we saw plenty of examples where people were encouraged to invest in cryptocurrency in all possible manners: famous Belgians who (allegedly) made a lot of money this way and encouraged you to do the same, spam messages and even via the social media pages of your own friends.
New: watch out for fake QR codes
What was new in 2022 is that the link in suspicious messages is sometimes replaced by a QR code. However, the result is the same: you are directed to a suspicious website where you are asked to enter your information. This is a particular risk for inattentive users. When you scan a QR code, you cannot really see which website you are redirected to. It's much more difficult to check the URL.
Here to stay
Finally, we notice that the same messages keep coming back every year. A short overview:
The most popular messages are still those that purport to come from government bodies. Annually recurring government notices are a great source of inspiration for scammers. They claim to come from the government's Finance Department around the time of tax return and they ask for additional info (preferably your bank account number) or promise you a refund. They also try to trick you by posing as the National Social Security Administration, the Pension Department, the National Office of Annual Vacations (ONVA/RJV), De Watergroep, the Crossroads Bank of Enterprises, etc. They follow the same calendar as the official notices.
eBox, Doccle, and My Citizen Profile are often misused. As the general public trusts these portals, and find it hard to identify fake portals, they're more likely to make mistakes. These posts appear non-stop throughout the year.
Banks, internet providers and the authentication platform Itsme® are constantly spoofed by criminals (using excuses like: "Click here to apply for a new card now for free; if you wait you'll have to pay" or "You have to re-authenticate your account to avoid it getting blocked"), as are all parcel delivery companies and well-known online shops. These "shops" will ask you to click on a link to track a package or to pay additional shipping costs. Messages from "parcel delivery companies" pop up every year in November and then quietly disappear after January.
Messages from "the police" were a constant this year. There are two stories that are most common: in the first scenario, you supposedly received a fine and are asked to pay online; in the second case, you are accused of possessing pornographic material and are extorted. You then receive what claims to be a convocation or subpoena from Europol or the Federal Police.
The latter is also called a sextortion scam and comes in different forms and languages. As part of the sextortion scam, you receive a message where the extortionists claim that they have hacked into your computer and taken intimate images of you watching porn. The extortionists threaten to distribute the images on the Internet unless you pay a fee.
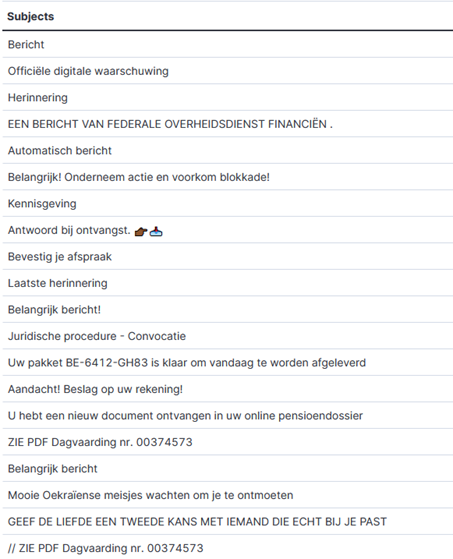
Top 20 messages to suspicious@safeonweb.be (subject line)